 IEEE/ICACT20230048 Slide.06
[Big Slide]
[YouTube]
IEEE/ICACT20230048 Slide.06
[Big Slide]
[YouTube]  Oral Presentation
Oral Presentation 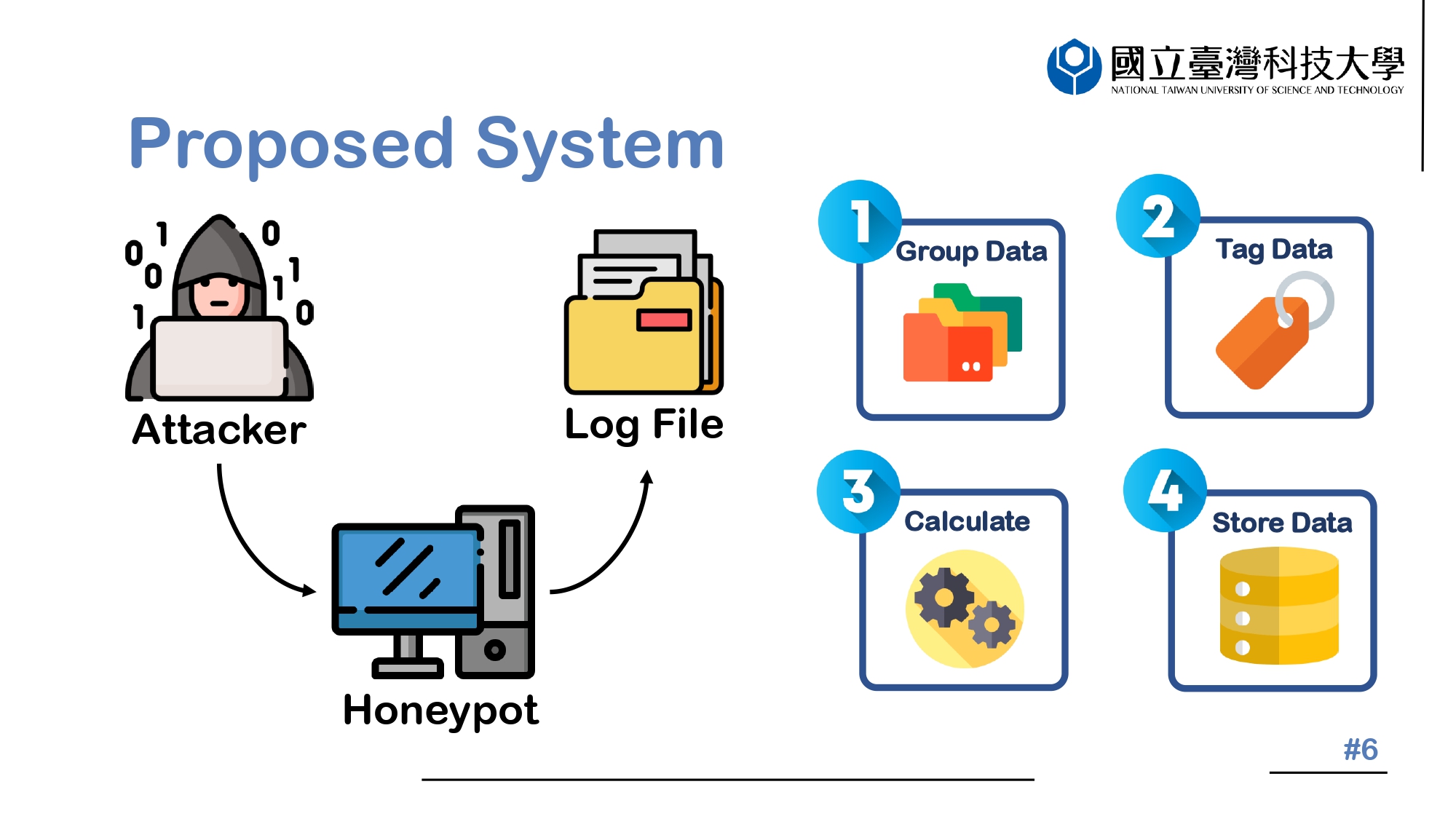
| Virual Oral Presentation Slide by Slide |
 IEEE/ICACT20230048 Slide.06
[Big Slide]
[YouTube]
IEEE/ICACT20230048 Slide.06
[Big Slide]
[YouTube] |
 Oral Presentation Oral Presentation |
|
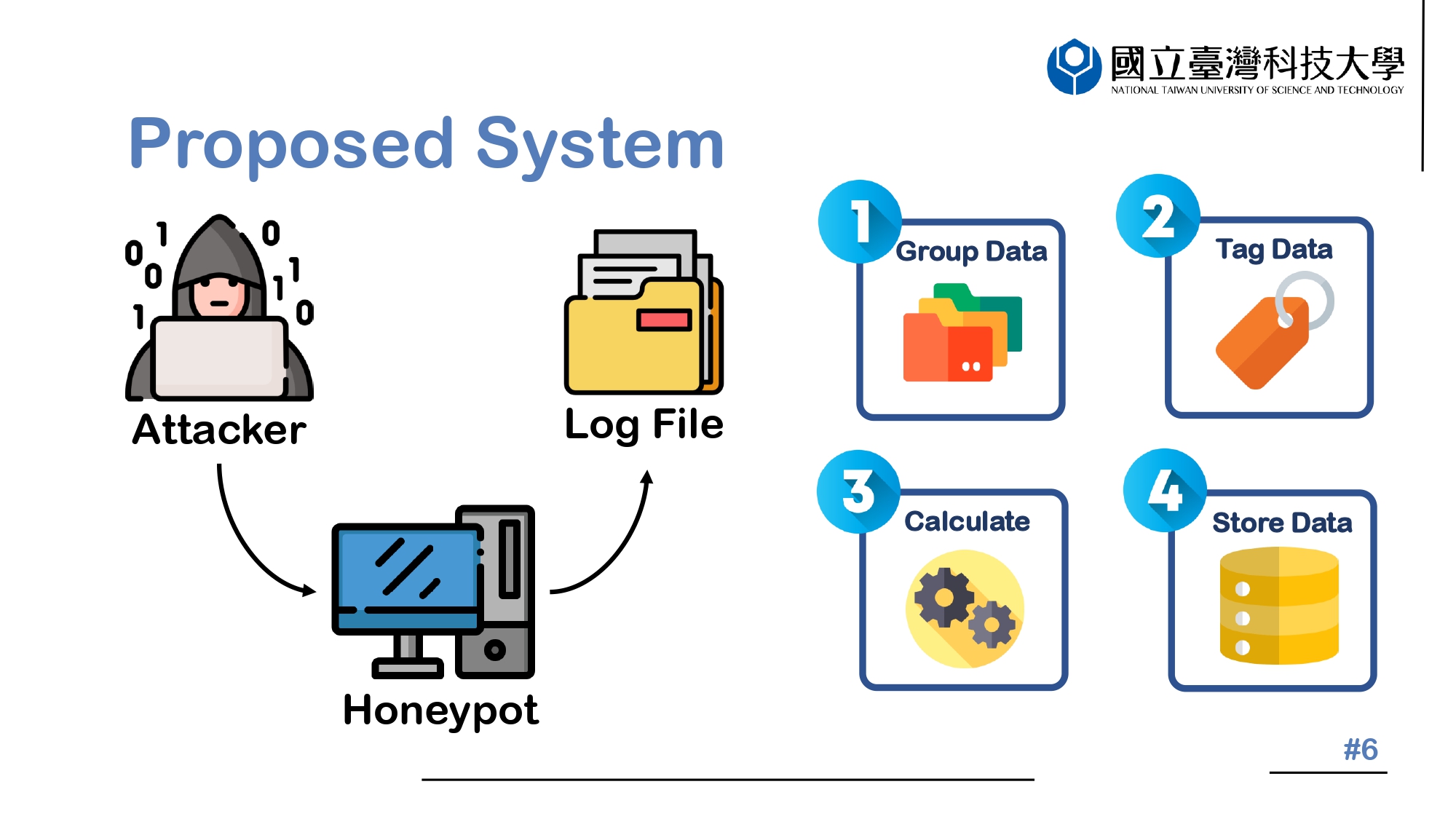 |
First, let's briefly describe the entire process. We set up a Honeypot to collect information from attackers, and the collected data is formed into multiple clusters using the K-means algorithm. Then, the attributes of each cluster are manually tagged through MITRE ATT&CK. The TF-IDF value of each payload is calculated, and the tagged data, data-related information, and TF-IDF calculation score are saved in the Session Table. | |
| [Go to Next Slide] |