 |
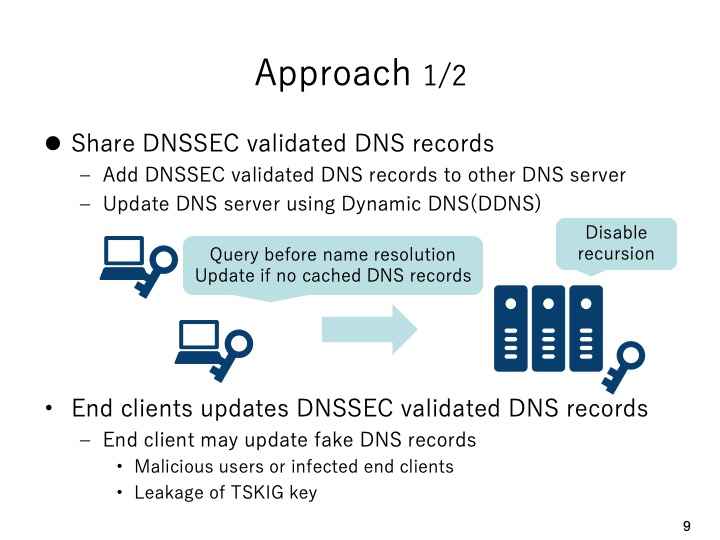
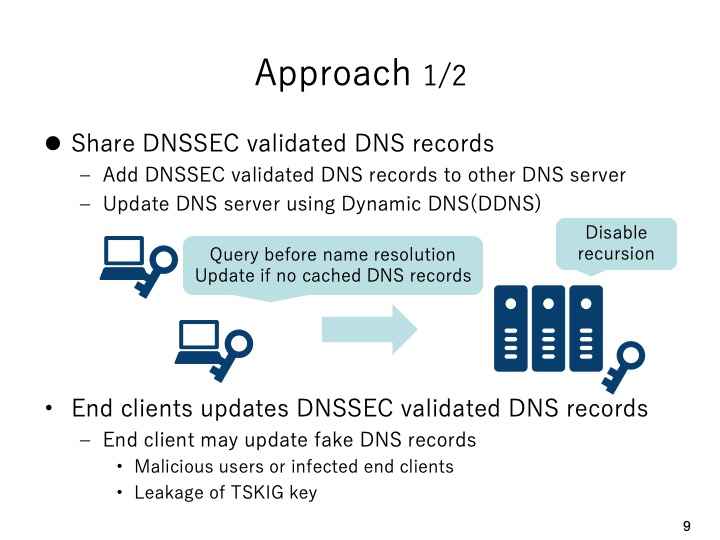
The first approach we considered is to share successfully DNSSEC validated DNS
resources records using a DNS sharing server. Each end client updates the successfully
validated DNS resource records to the DNS sharing server using dynamic DNS update.
Then each end client queries the DNS sharing server first in the domain name resolution
and if there is no cache hit the end client will continue to query the external cache DNS
server. However, this approach has a critical flaw that the malicious users or infected
clients may add fake DNS resource records to the DNS sharing server. Moreover,
although TSIG will be used in the dynamic DNS update, when the TSIG key is stolen it
can be used maliciously. |
 IEEE/ICACT20220132 Slide.10
[Big Slide]
[YouTube]
IEEE/ICACT20220132 Slide.10
[Big Slide]
[YouTube]  Oral Presentation
Oral Presentation 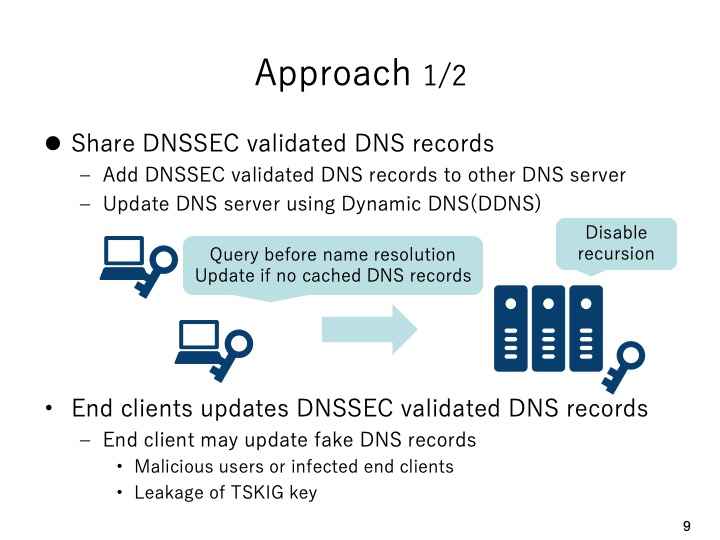
 IEEE/ICACT20220132 Slide.10
[Big Slide]
[YouTube]
IEEE/ICACT20220132 Slide.10
[Big Slide]
[YouTube]  Oral Presentation
Oral Presentation