 IEEE/ICACT20230048 Slide.13
[Big Slide]
[YouTube]
IEEE/ICACT20230048 Slide.13
[Big Slide]
[YouTube]  Oral Presentation
Oral Presentation 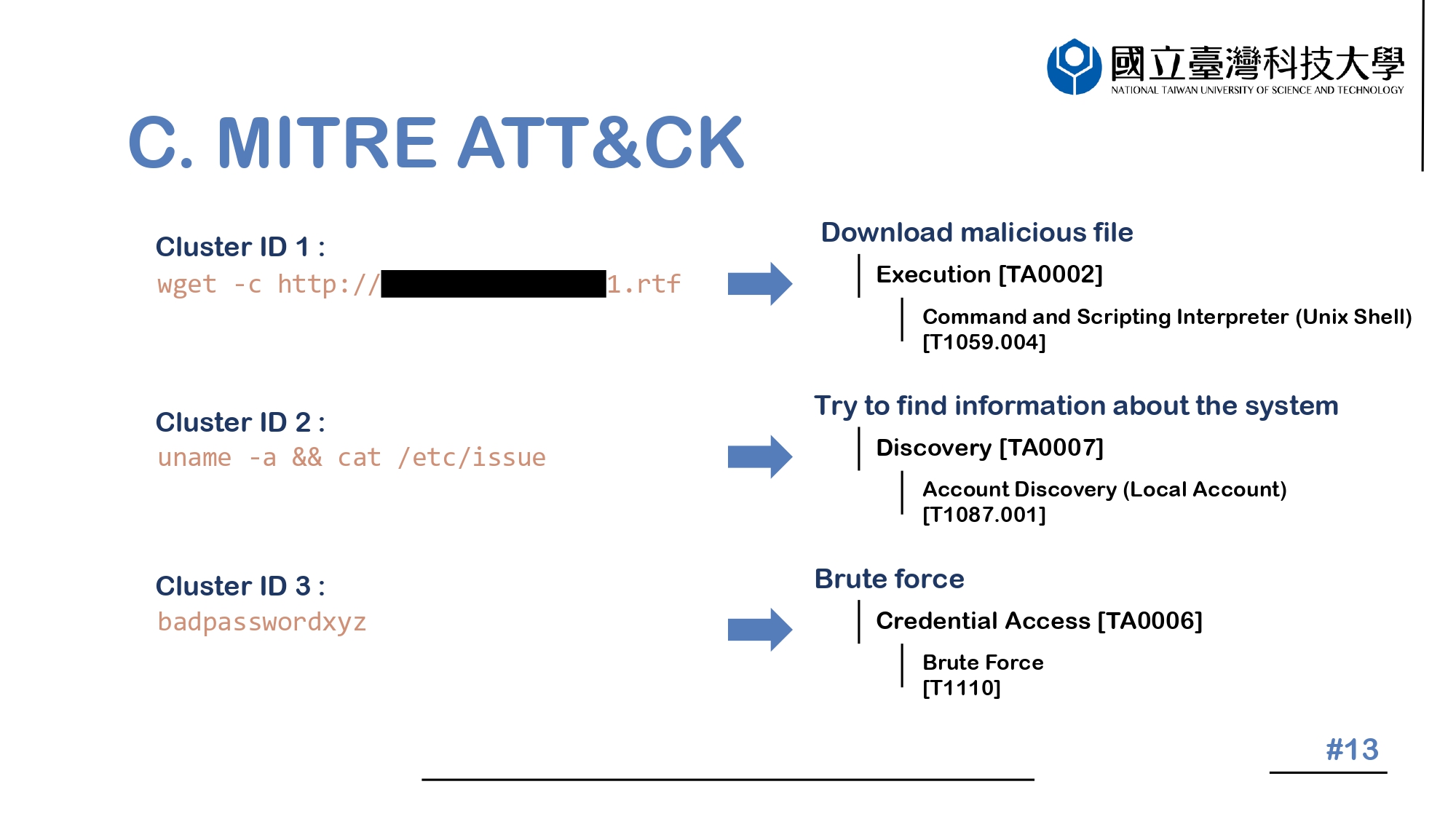
| Virual Oral Presentation Slide by Slide |
 IEEE/ICACT20230048 Slide.13
[Big Slide]
[YouTube]
IEEE/ICACT20230048 Slide.13
[Big Slide]
[YouTube] |
 Oral Presentation Oral Presentation |
|
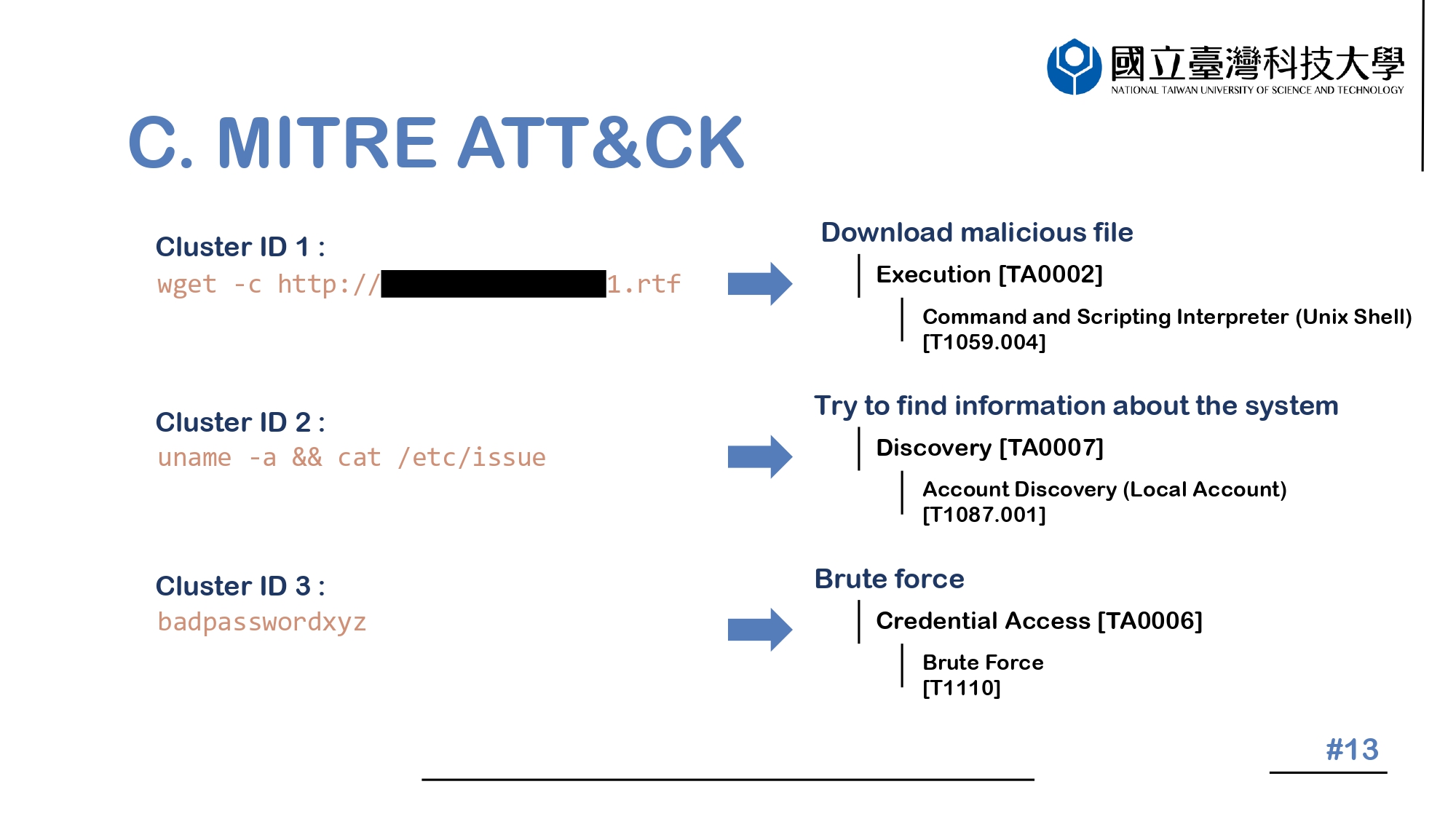 |
We can see, Cluster 1 is Download malicious fileŁ¬so its Tactic is Execution and its Subtechnique is Command and Scripting Interpreter. Cluster 2 is try to find information about the systemŁ¬so its Tactic is Discovery and its Subtechnique is Account Discovery (Local Account). Cluster 3 is Brute forceŁ¬so its Tactic is Credential Access and its Subtechnique is Brute Force. | |
| [Go to Next Slide] |