 |
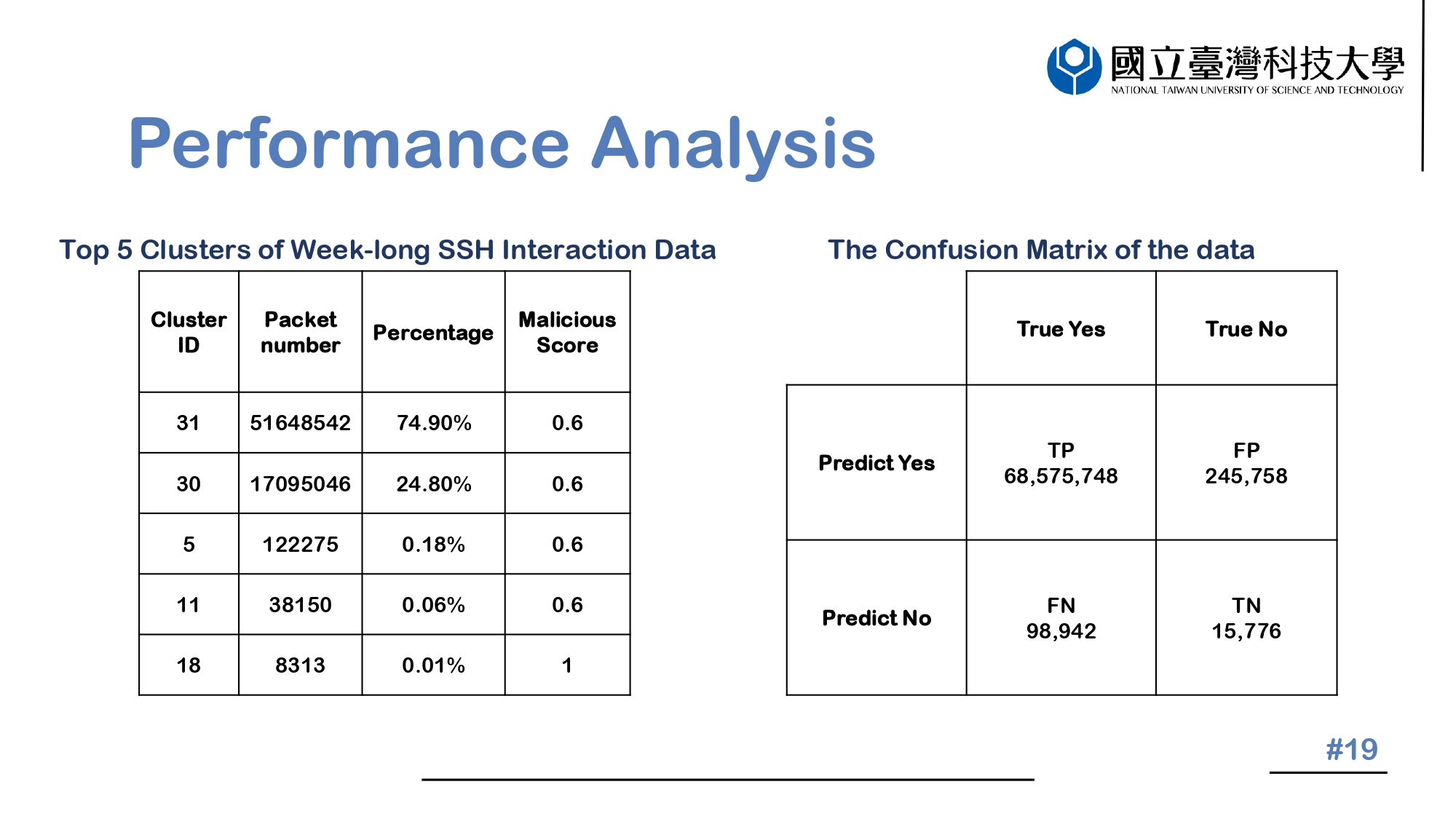
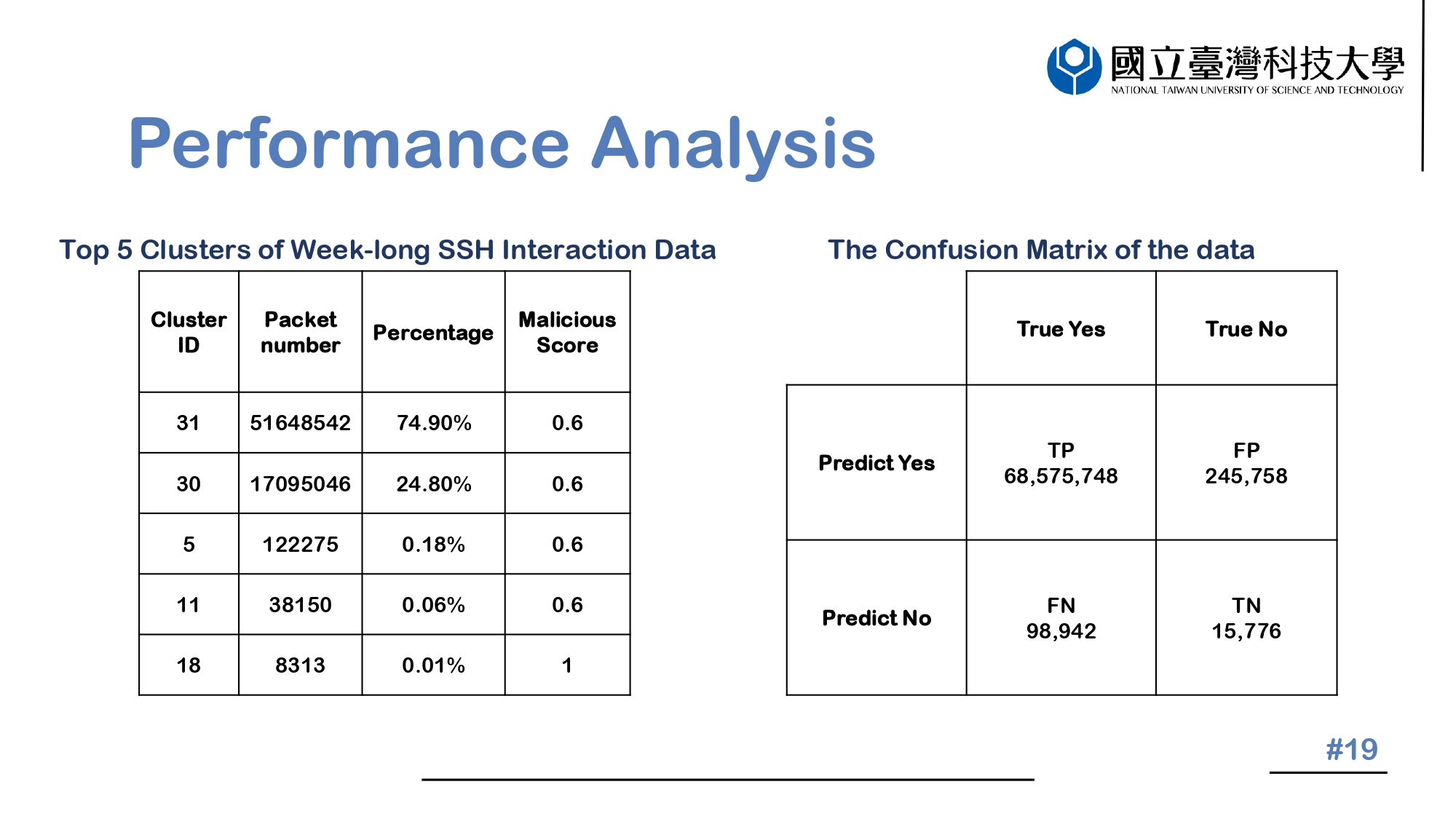
The table on the left shows the Top 5 Clusters of Week-long SSH Interaction Data. Cluster ID: 31 and Cluster ID: 30 have higher proportions and respectively represent "Brute force account password" and "Simple SSH connection". The command of "connection" takes up a large portion of the attack behavior, however the attack behaviors that make up a small proportion have a higher malicious score.
On the right is the confusion matrix of the data through the K-means algorithm. TP stands for the number of packets that are accurately clustered after the algorithm, FP for the number of packets wrongly clustered, FN for the number of packets that could not be clustered but could be classified into clusters after the algorithm's judgement, and TN for the number of packets that could not be clustered after the algorithm's judgement.
|
 IEEE/ICACT20230048 Slide.19
[Big Slide]
[YouTube]
IEEE/ICACT20230048 Slide.19
[Big Slide]
[YouTube]  Oral Presentation
Oral Presentation 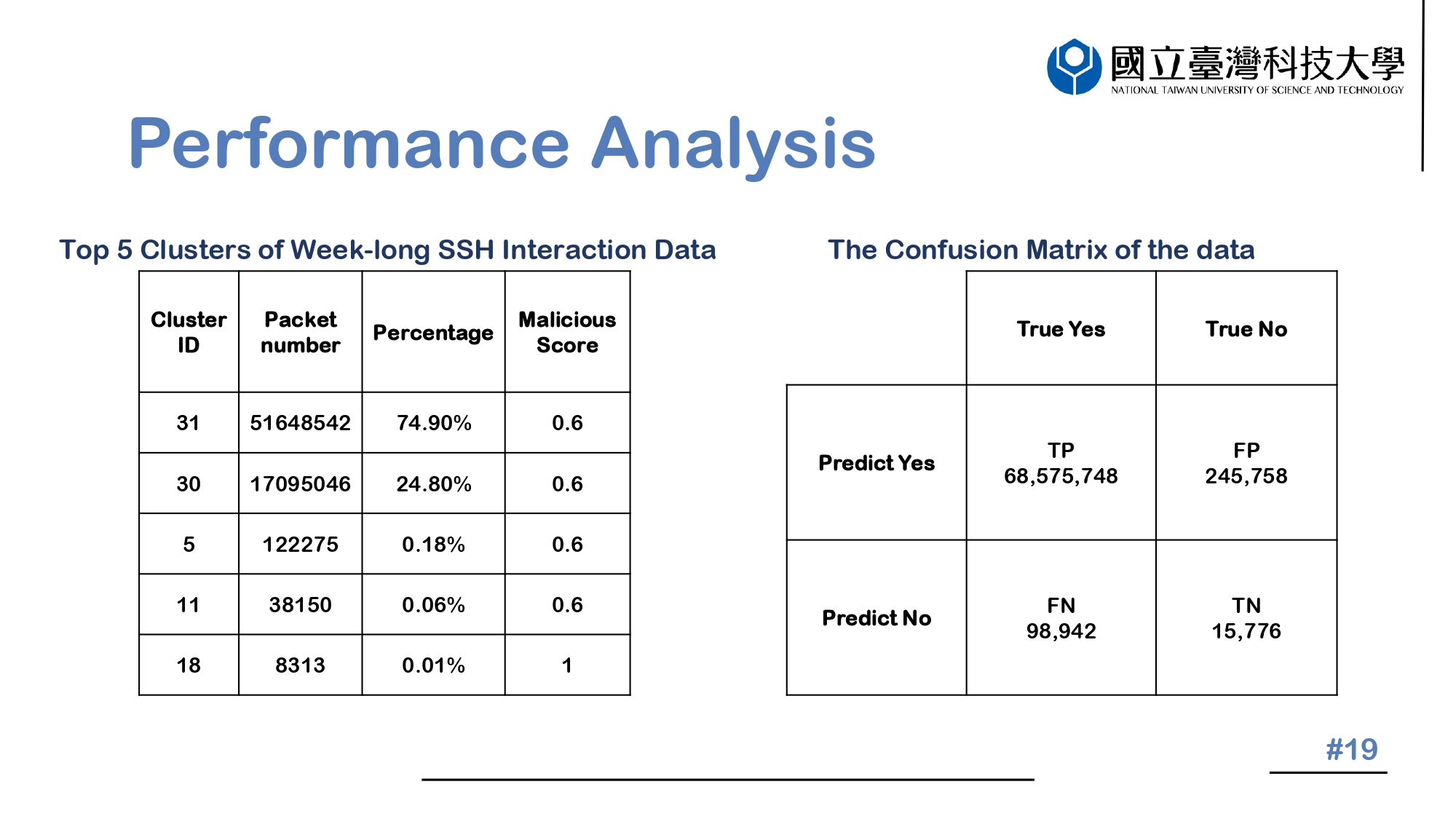
 IEEE/ICACT20230048 Slide.19
[Big Slide]
[YouTube]
IEEE/ICACT20230048 Slide.19
[Big Slide]
[YouTube]  Oral Presentation
Oral Presentation