 ICACT20230048 Slide.22
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.22
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
 |
Thank you for listening to my presentation. I appreciate the opportunity to share my research with you all. I hope the information I presented was informative and useful. Your feedback and questions have helped me further understand and improve my work. Thank you.
|
 ICACT20230048 Slide.21
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.21
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
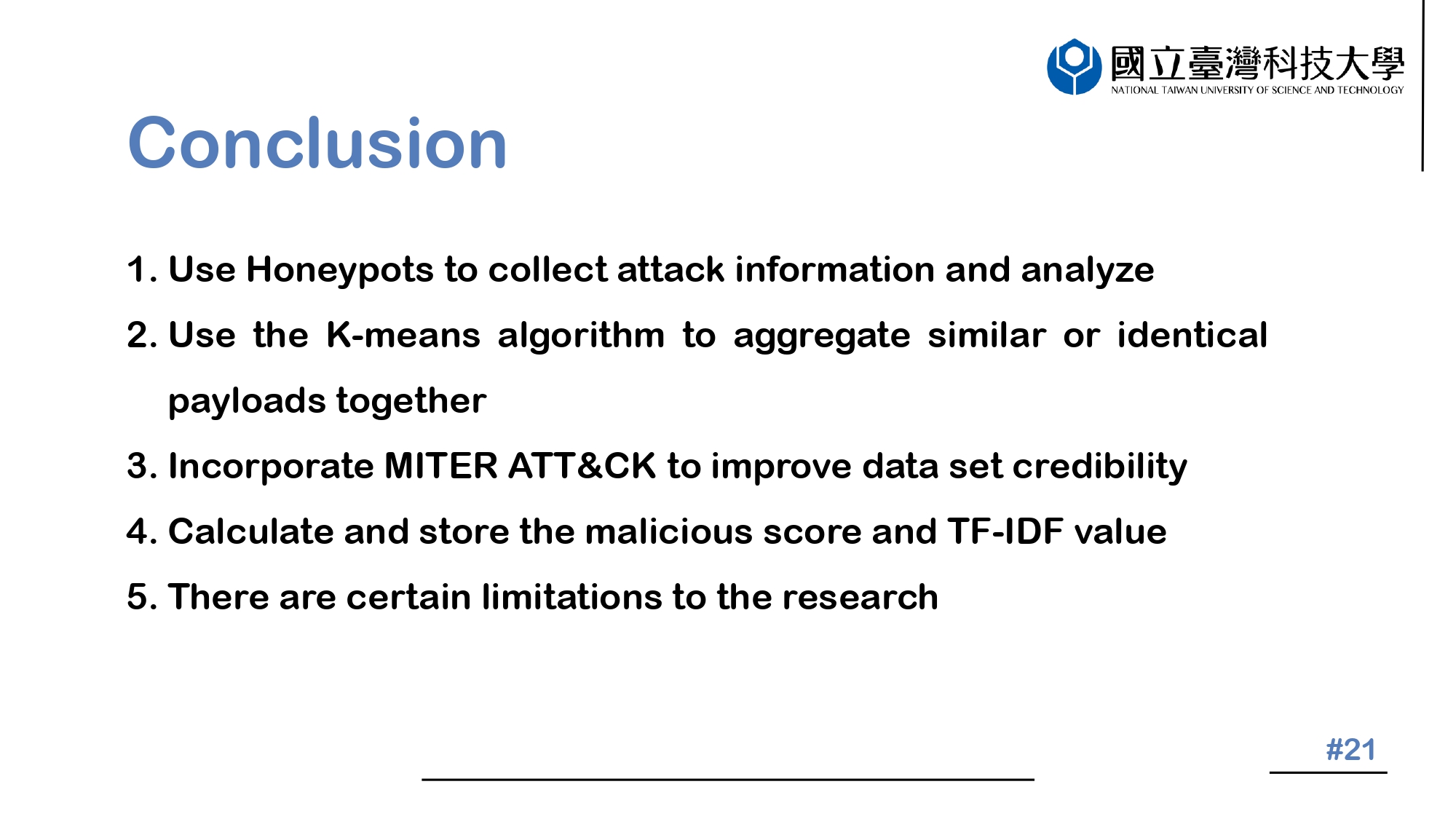 |
In conclusion, we have developed a system that integrates data analysis, machine learning, manual labeling, TFIDF weighting techniques, and a malicious score. The use of K-means algorithms and MITRE ATT&CK TTP tags allows for quick identification of high-threat attacks, which is valuable for further research. Furthermore, dividing large-scale attacks into smaller groups helps with data labeling, enabling systematic categorization and storage of data as Session Table. Although the proposed system achieved a clustering accuracy of 99.5%, and the source is labeled to provide a reliable dataset with realistic examples, the experiments in this study are not applicable to other situations.
|
 ICACT20230048 Slide.20
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.20
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
 |
The final part is conclusion.
|
 ICACT20230048 Slide.19
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.19
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
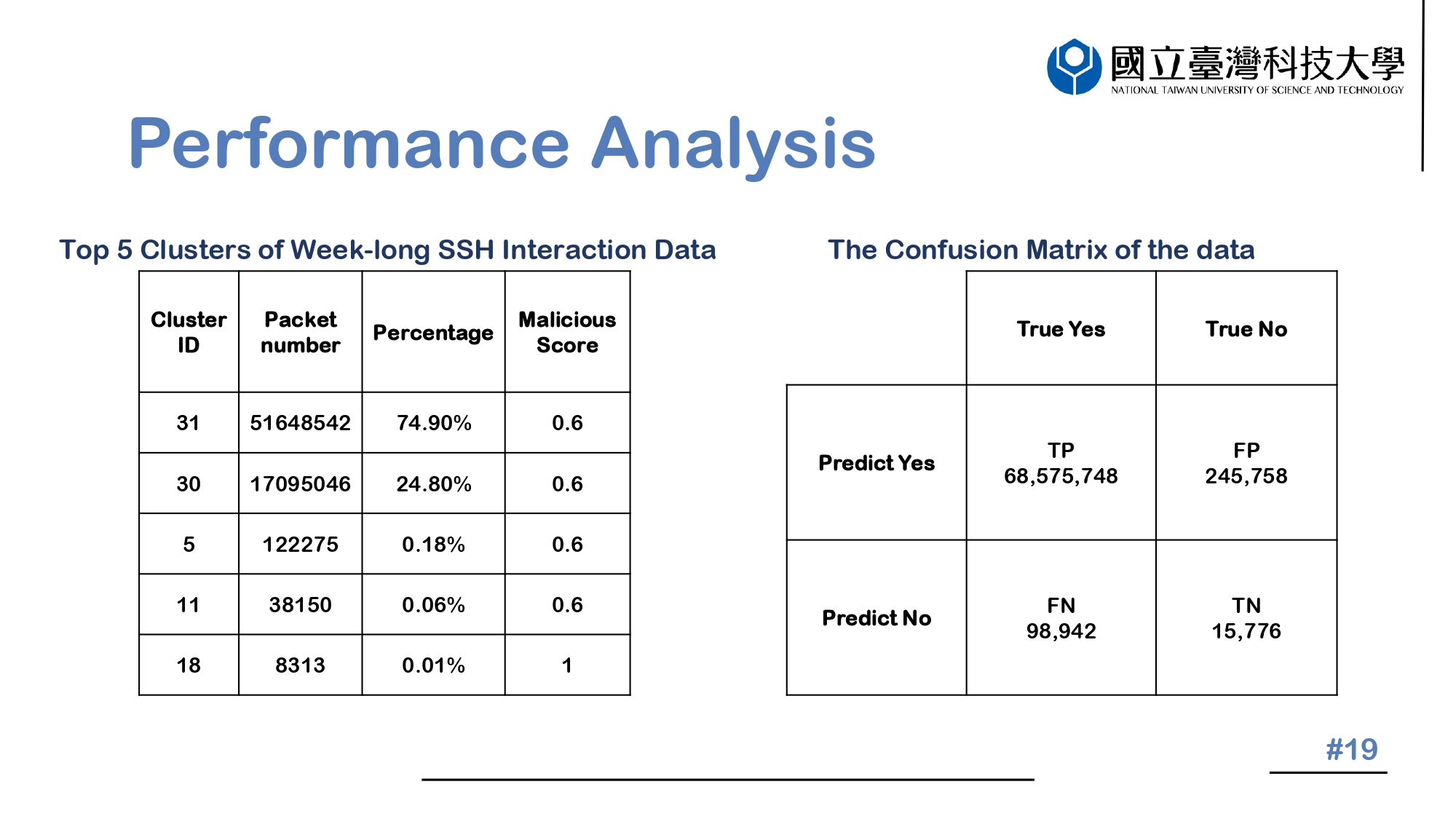 |
The table on the left shows the Top 5 Clusters of Week-long SSH Interaction Data. Cluster ID: 31 and Cluster ID: 30 have higher proportions and respectively represent "Brute force account password" and "Simple SSH connection". The command of "connection" takes up a large portion of the attack behavior, however the attack behaviors that make up a small proportion have a higher malicious score.
On the right is the confusion matrix of the data through the K-means algorithm. TP stands for the number of packets that are accurately clustered after the algorithm, FP for the number of packets wrongly clustered, FN for the number of packets that could not be clustered but could be classified into clusters after the algorithm's judgement, and TN for the number of packets that could not be clustered after the algorithm's judgement.
|
 ICACT20230048 Slide.18
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.18
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
 |
The next part is performance analysis.
|
 ICACT20230048 Slide.17
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.17
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
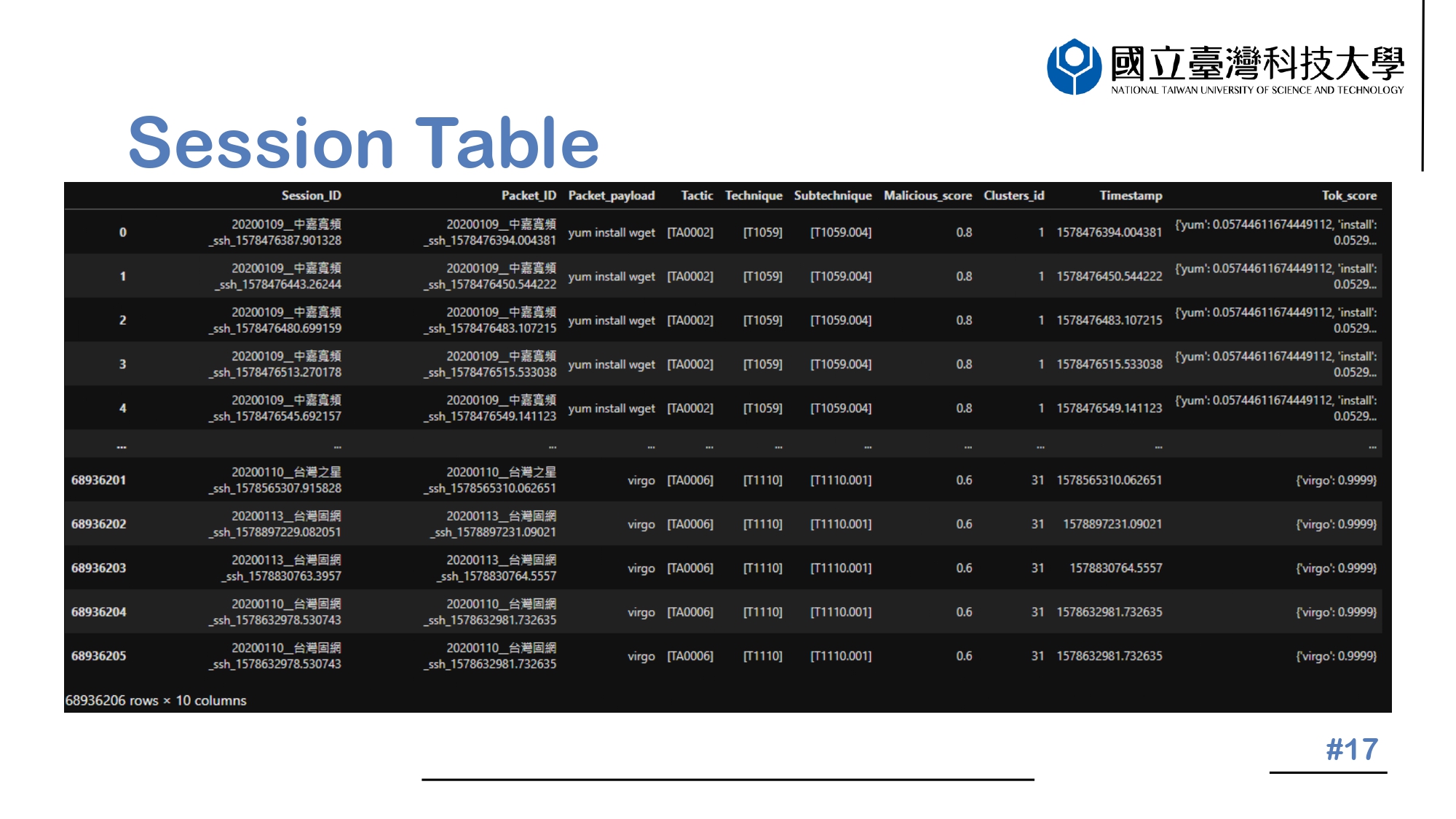 |
Finally, the information is presented in the form of a session table, as illustrated in the accompanying figure. To identify the Packet_ID, we utilize the timestamp as the key element. The Session_ID, on the other hand, is derived from the combination of the session_timestamp, the src_ip, and the src_port.
|
 ICACT20230048 Slide.16
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.16
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
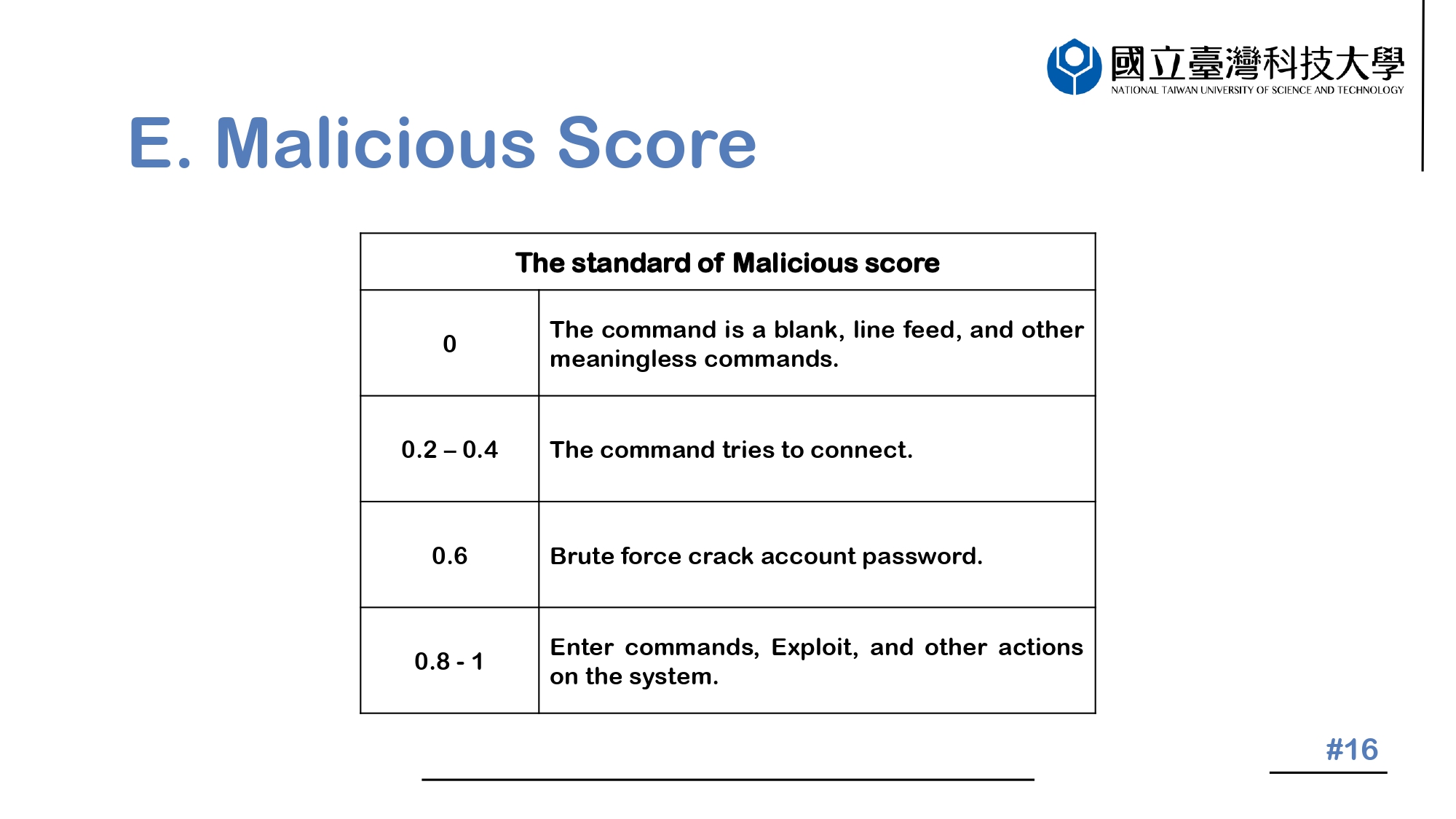 |
Each group is assigned a malicious score that reflects the level of harm it poses. To ensure a consistent and accurate evaluation, a unified standard for the malicious score has been established by a collaboration of personnel from three separate institutions in Taiwan. The criteria for each score is presented as follows.
|
 ICACT20230048 Slide.15
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.15
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
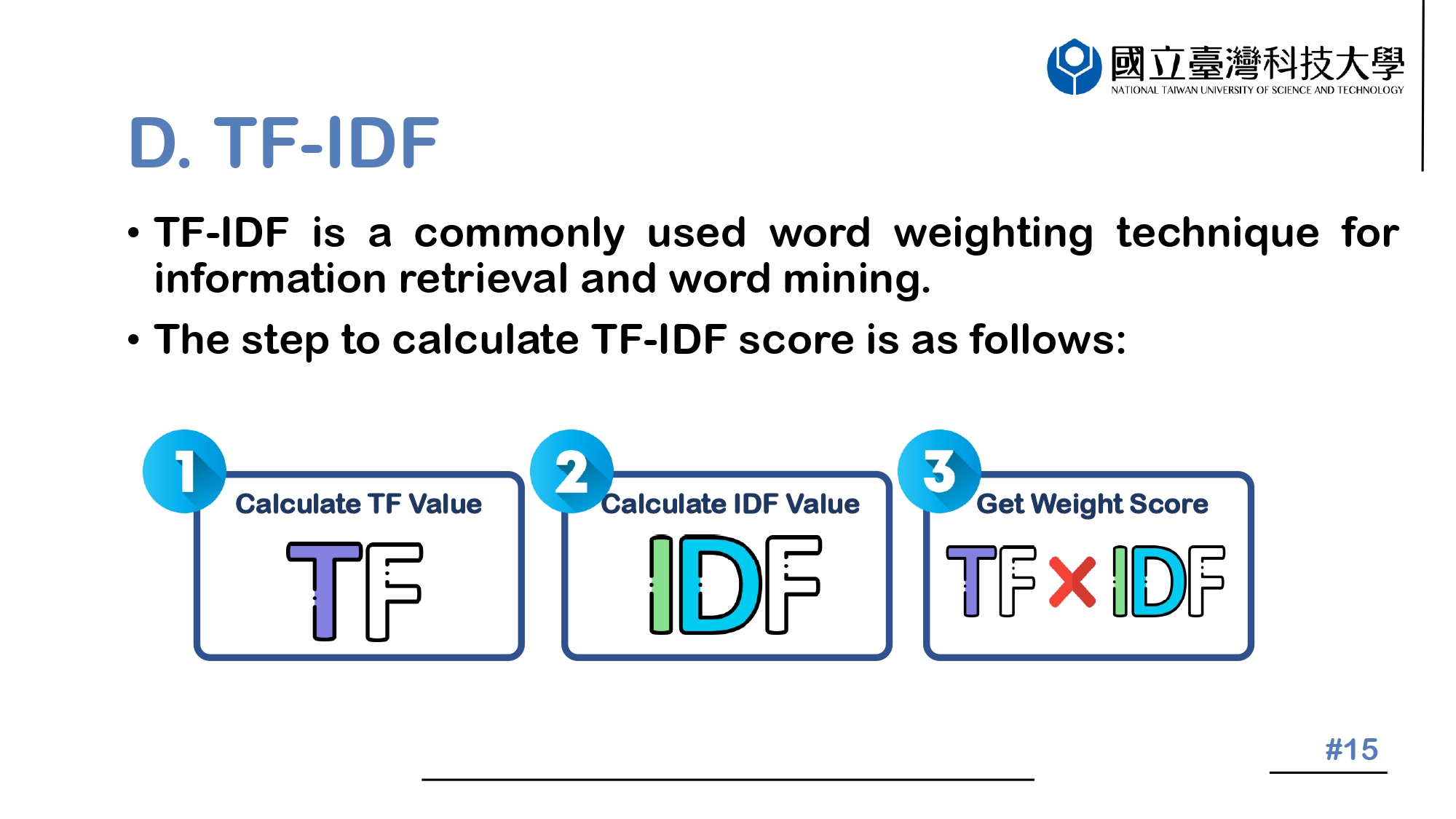 |
TFIDF is a commonly used word weighting technique for information retrieval and word mining.
The step to calculate TF-IDF score is as follows:
First, Term Frequency (TF) calculates the number of times a word appears in a single Payload.
Second, Inverse Document Frequency (IDF) estimates the number of times the word appears in all Payloads.
Finally, the two are multiplied to obtain a weighted score.
|
 ICACT20230048 Slide.14
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.14
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
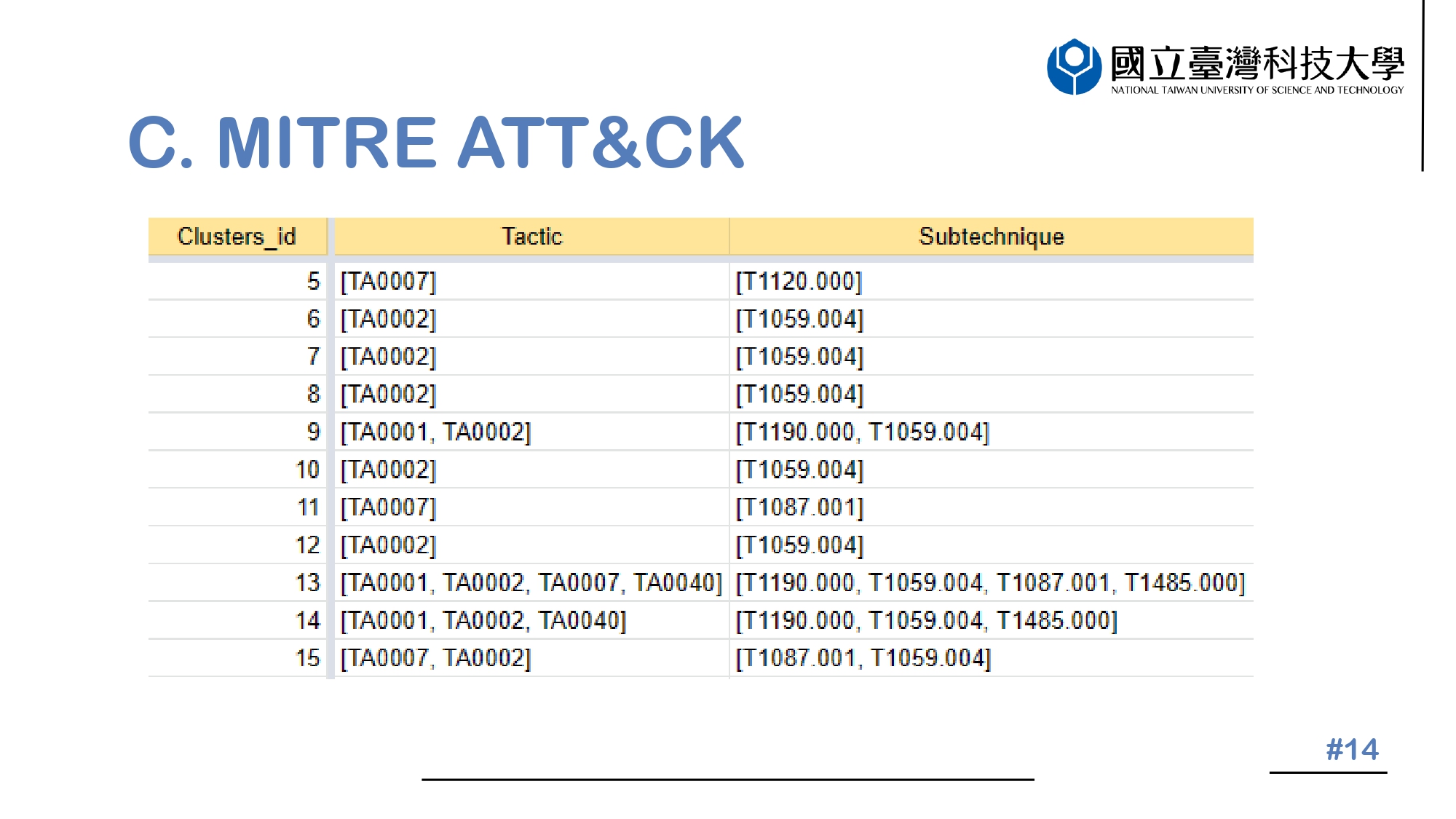 |
The picture before us visually represents the situation that we have marked and studied. Upon close examination, we can observe that in some instances, clusters consist of more than a single entity. This is due to the existence of payloads created with multiple instructions linked together.
|
 ICACT20230048 Slide.13
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.13
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
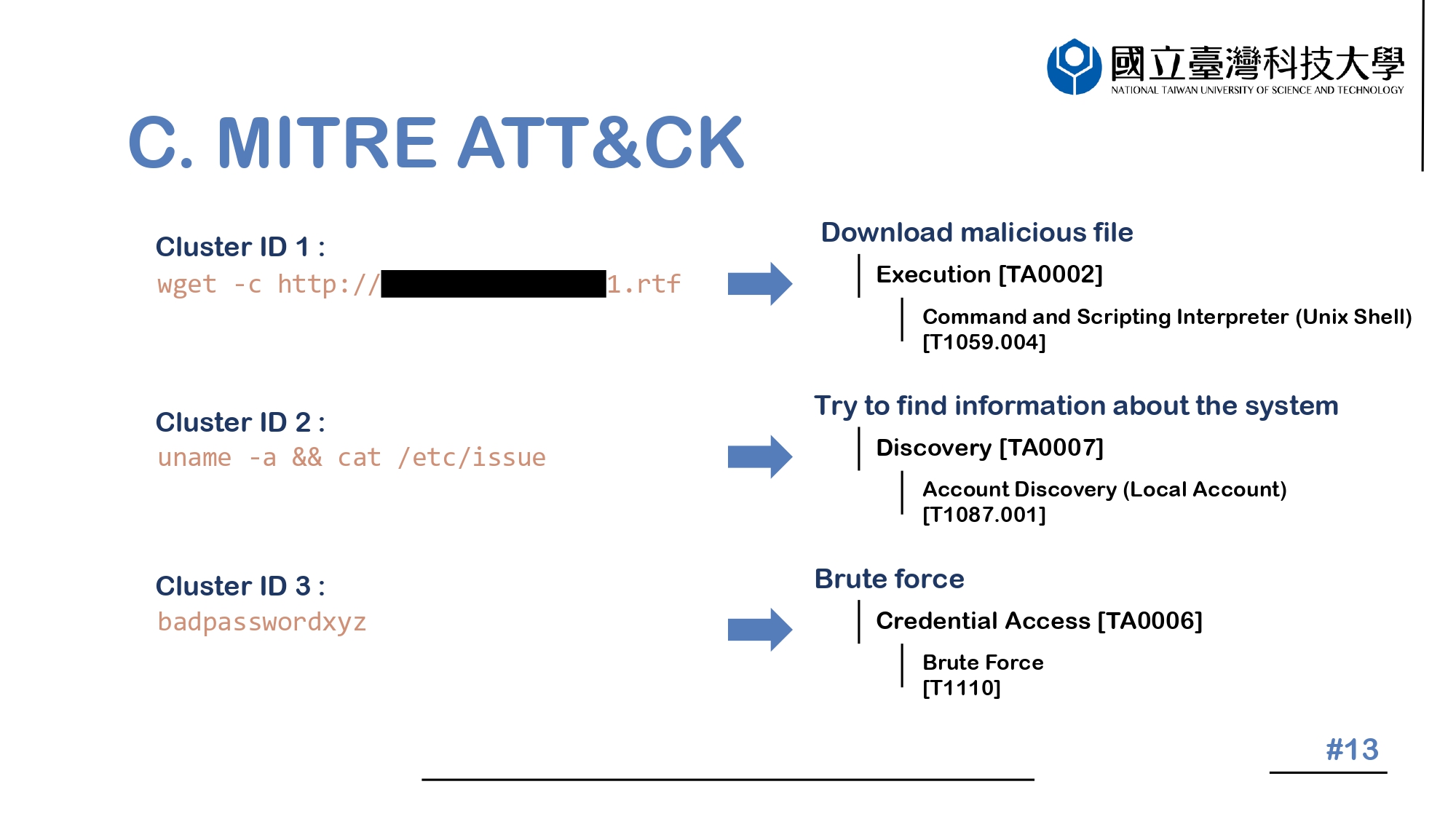 |
We can see, Cluster 1 is Download malicious file,so its Tactic is Execution and its Subtechnique is Command and Scripting Interpreter.
Cluster 2 is try to find information about the system,so its Tactic is Discovery and its Subtechnique is Account Discovery (Local Account).
Cluster 3 is Brute force,so its Tactic is Credential Access and its Subtechnique is Brute Force.
|
 ICACT20230048 Slide.12
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.12
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
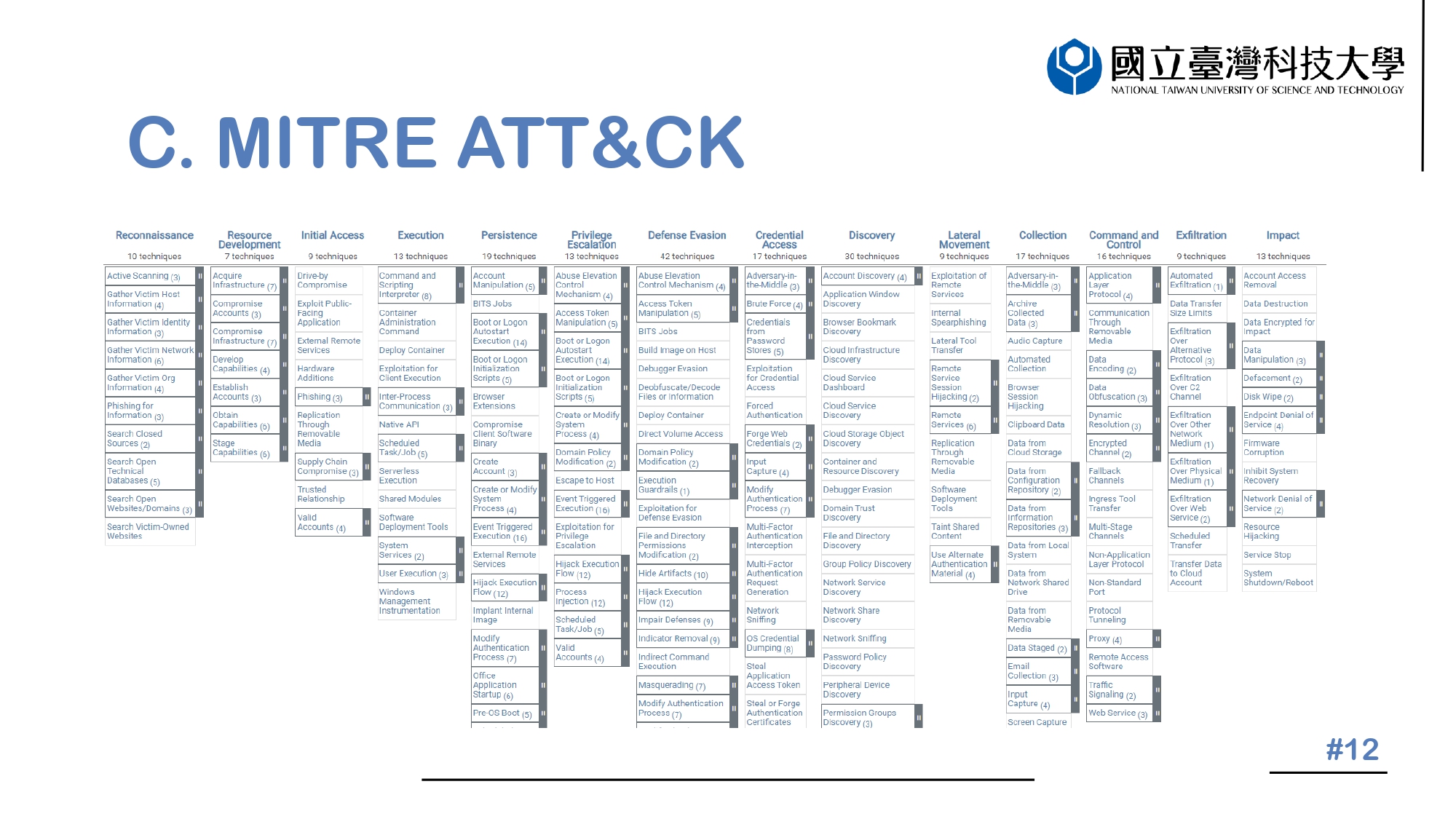 |
To label attack behavior, we use MITER ATT&CK. MITER ATT&CK is a knowledge base that shares cyber adversary behavior and attack lifecycle. It will be updated regularly with new types of attacks, which allows it to represent classified attacks more systematically. In MITER ATT&CK matrix, attack methods are classified by tactics, subtechniques, and procedures, or TTP for short, which can let security researchers easily recognize suspicious behavior. Our system also uses MITER ATT&CK TTP to label the attack behavior.
|
 ICACT20230048 Slide.11
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.11
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
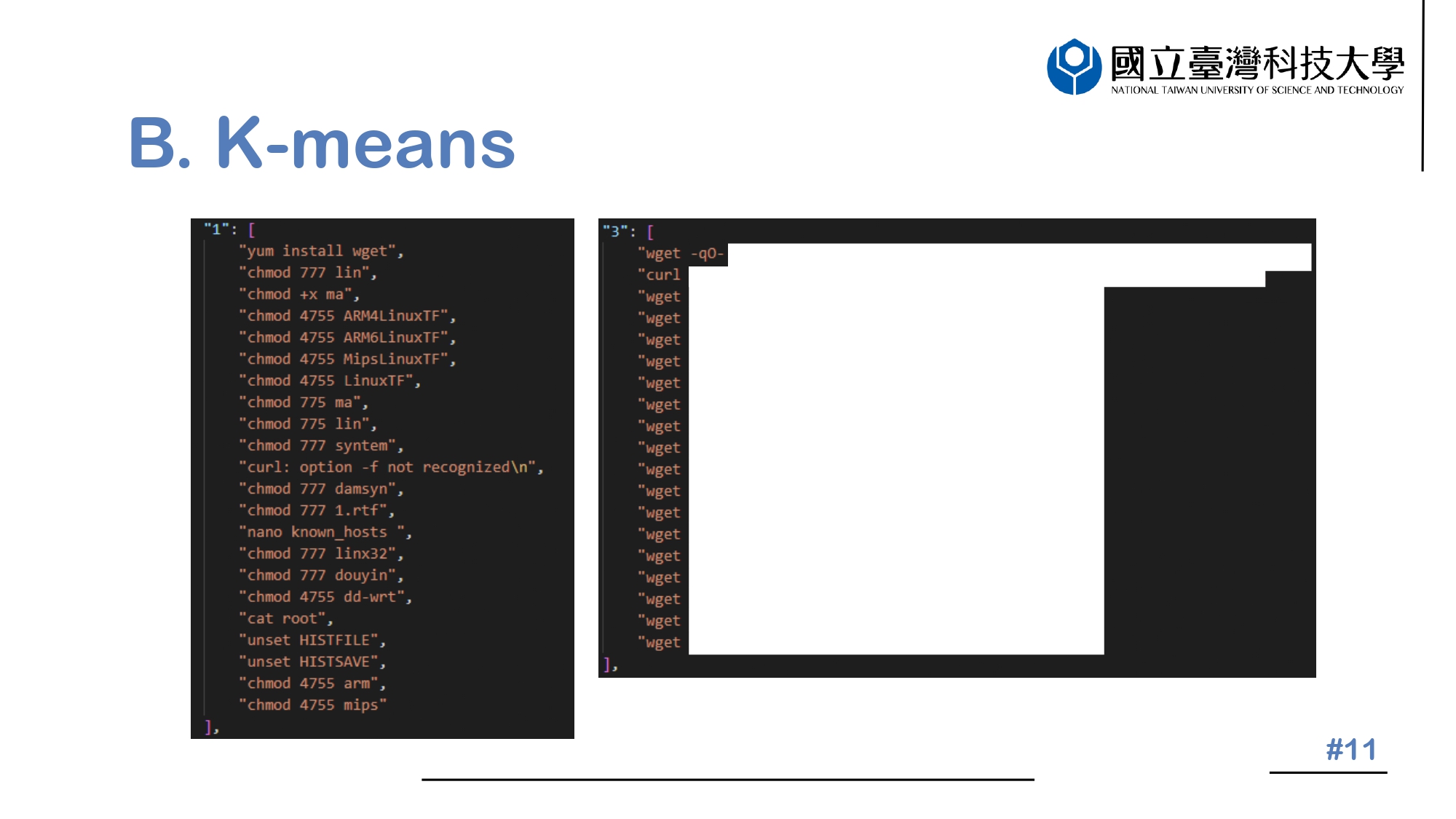 |
This graph shows the detailed information about what is included inside each of the two clusters, Cluster 1 and Cluster 3. In particular, Cluster 1 is mainly focused on altering the permissions associated with files, while Cluster 3 is devoted to downloading files from various sources.
|
 ICACT20230048 Slide.10
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.10
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
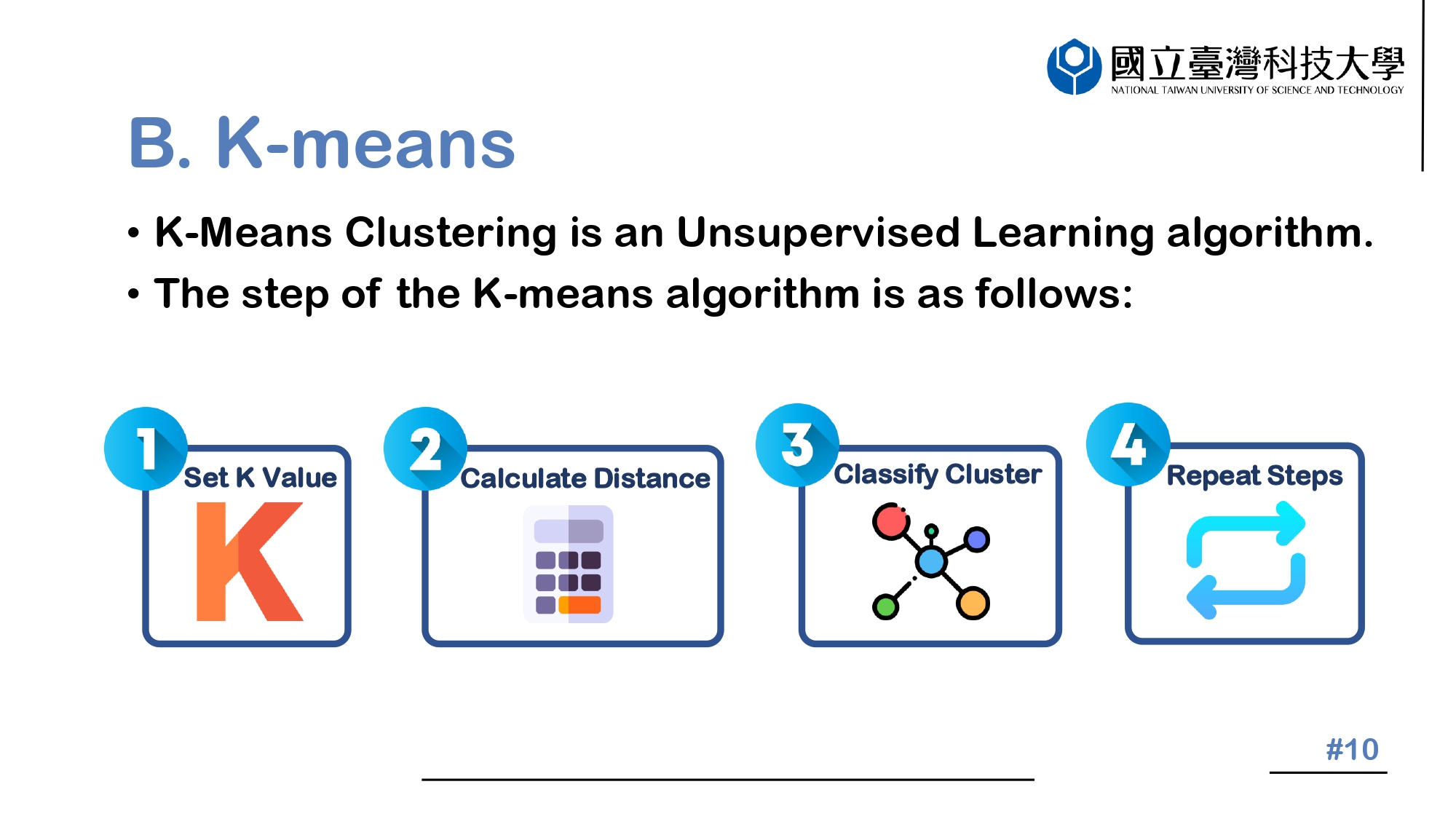 |
K-means algorithm is an unsupervised learning algorithm.
The processing flow includes the following: 1. The parameter K is first set, used as the number of cluster centers in the vector. 2. The cluster center is scattered in the vector space for each data. Calculate the shortest Euclidean distance between each data to all cluster centers. 3. Take the cluster with the shortest distance for each data and classify it as that. 4. Finally, repeat steps 2 and 3. Finish until all data points stay the same from the cluster center.
|
 ICACT20230048 Slide.09
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.09
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
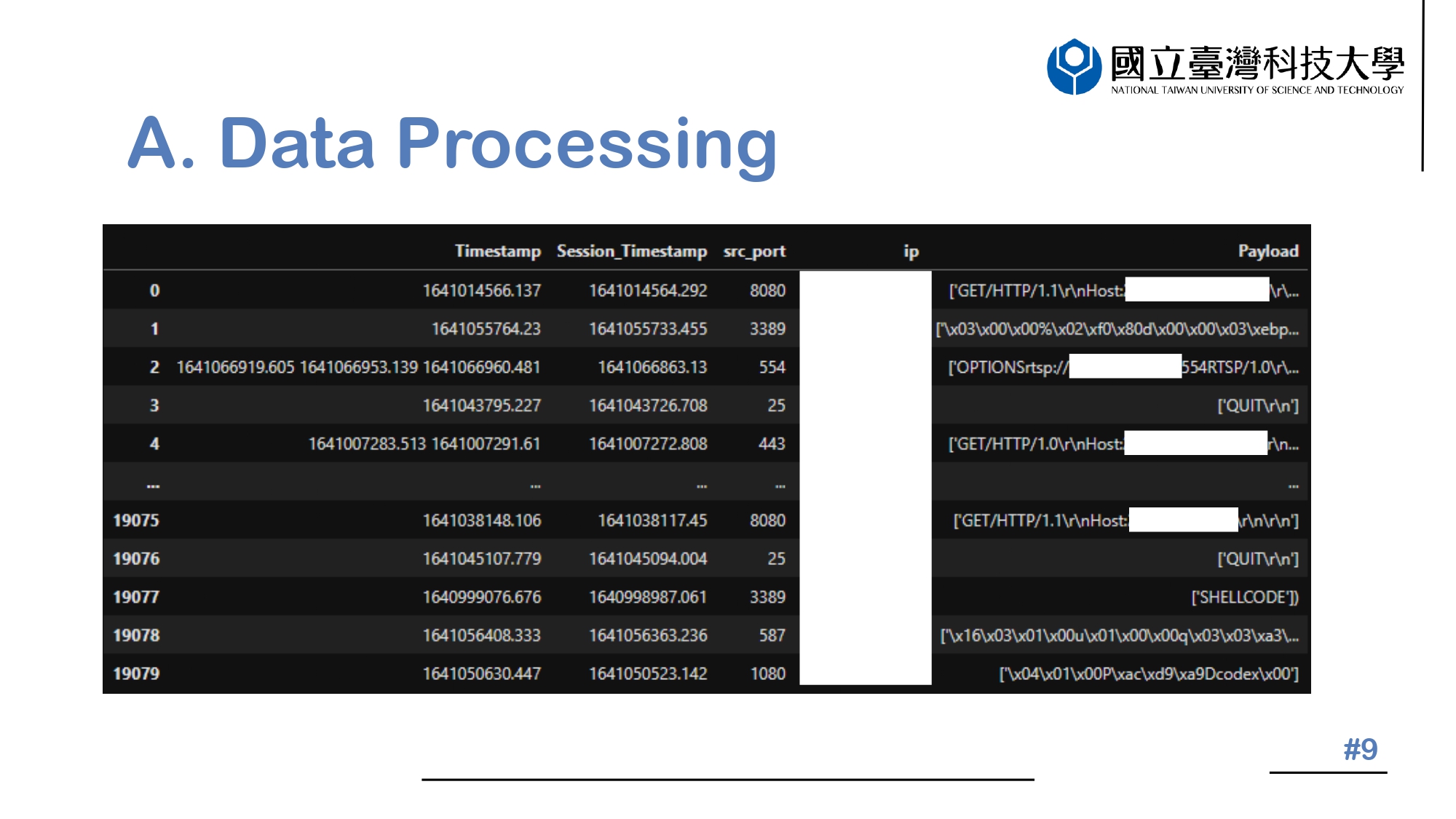 |
The figure we have shown you is a processed Dataframe that has been obtained from the Log File. It is visible to us that we have selected timestamp, session_timestamp, src_port, src_ip, and Payload from the Log File in order to further analyze it. With this data frame, we can now take a look at the information that has been extracted, and use this to better understand the content of the Log File.
|
 ICACT20230048 Slide.08
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.08
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
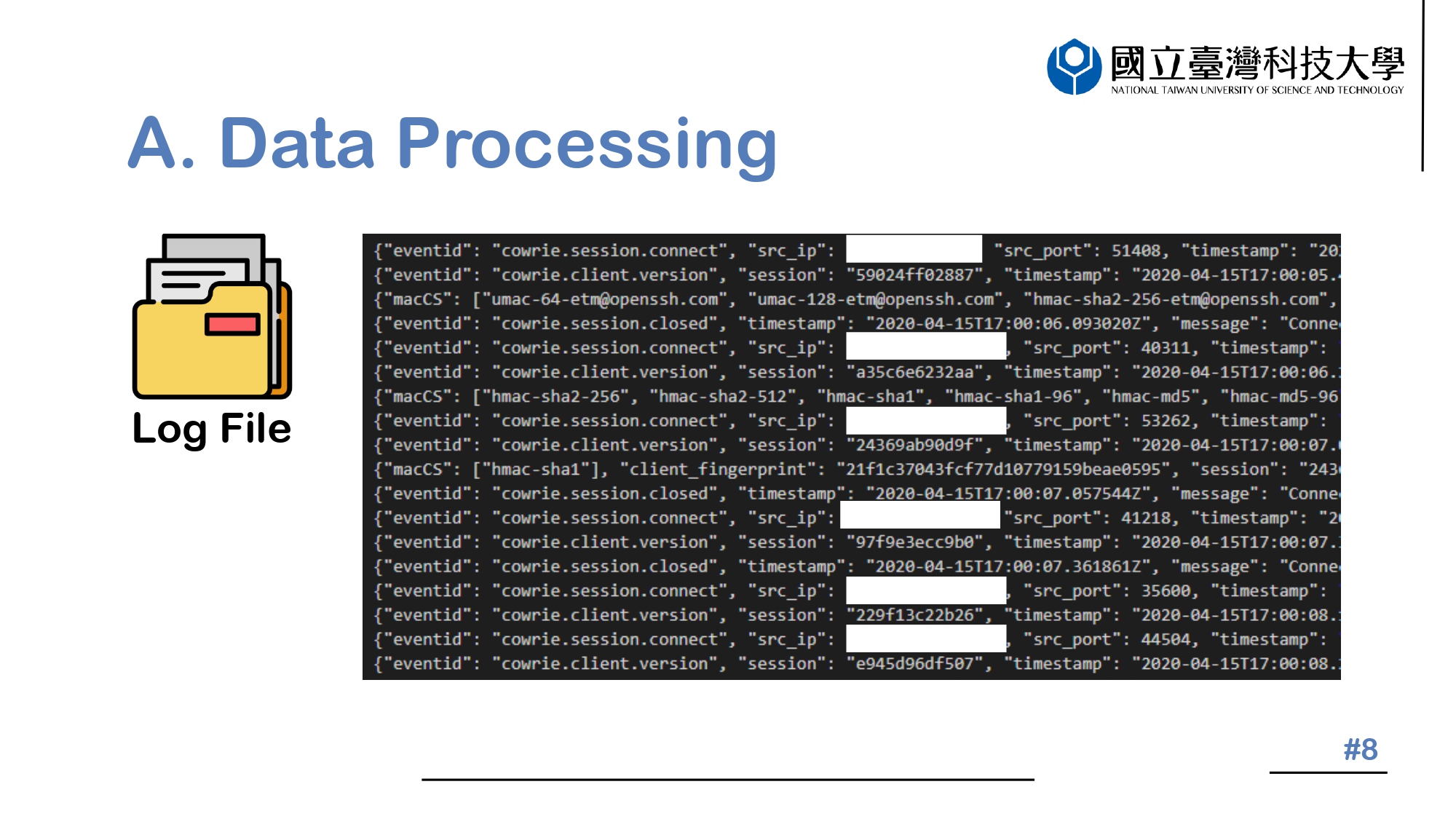 |
The diagram illustrates the contents of the Log File, which is in JSON format. Upon studying the diagram carefully, we can detect that some identifying information, such as timestamp and src_ip, will be chosen and stored in the Dataframe for further manipulation or analysis.
|
 ICACT20230048 Slide.07
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.07
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
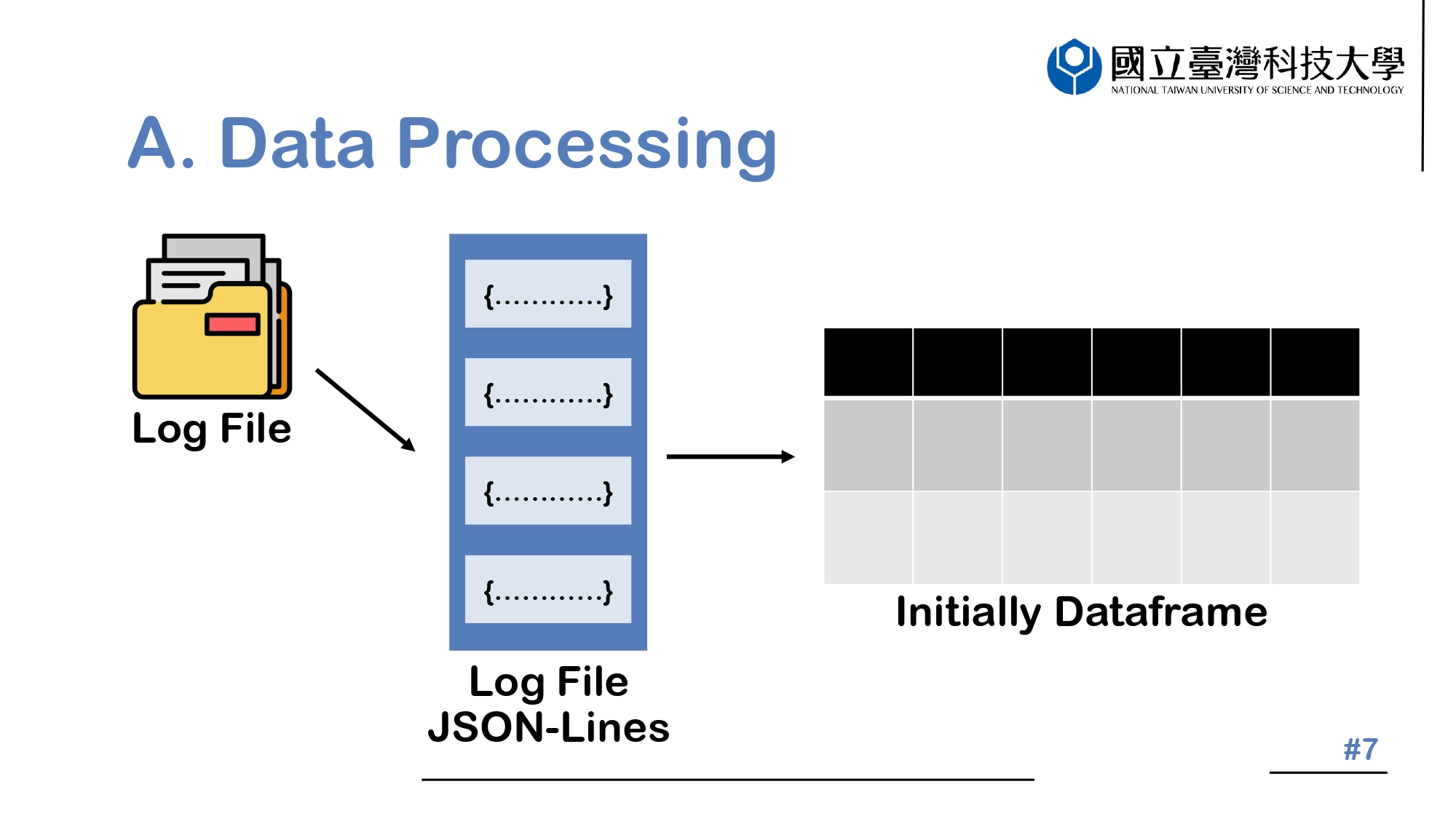 |
The Log File is presented in JSON-format in the Data Processing area. In order to make it easier to understand and interpret, we will first need to clean up the file and organize it into a Dataframe format.
|
 ICACT20230048 Slide.06
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.06
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
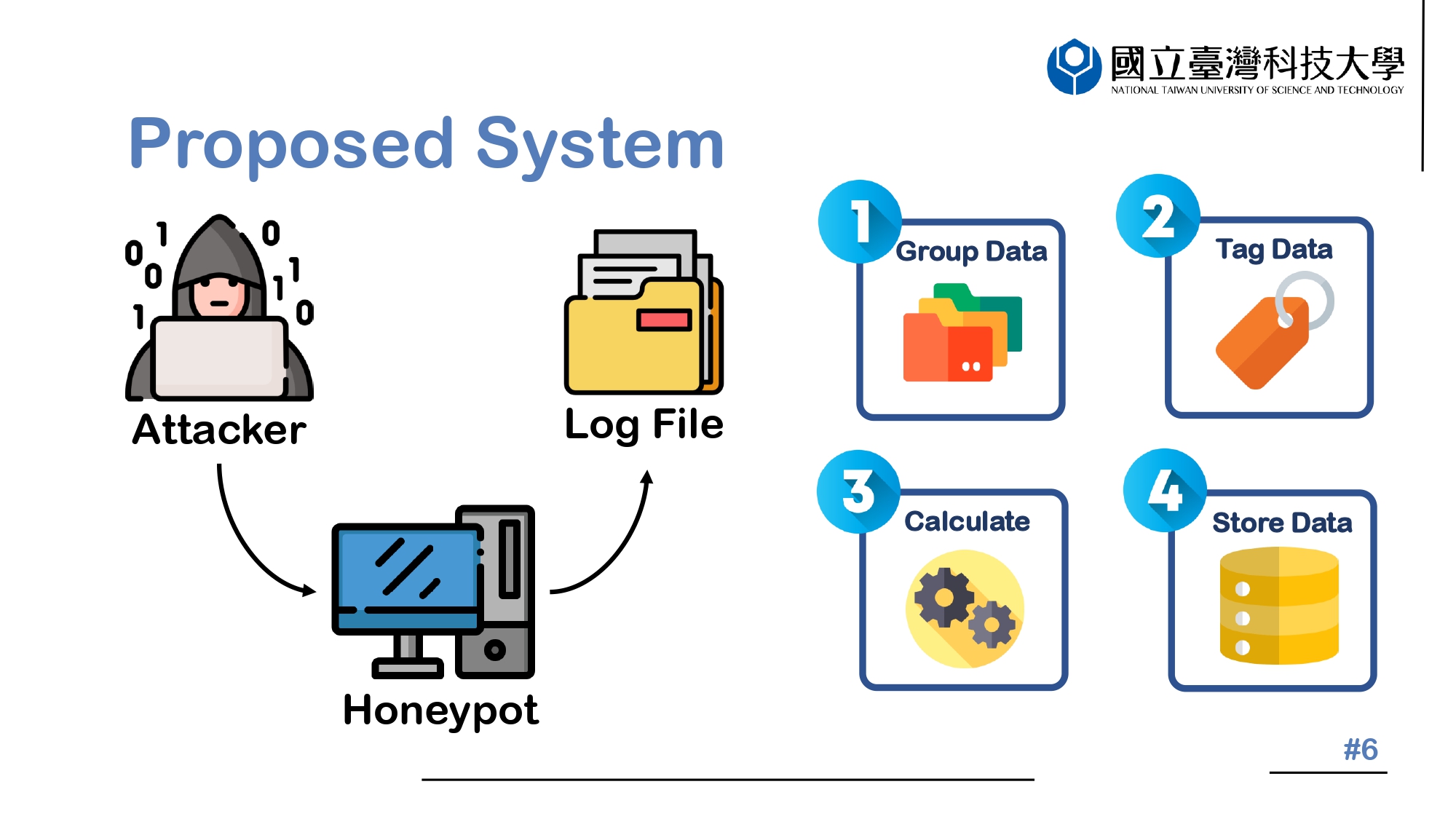 |
First, let's briefly describe the entire process. We set up a Honeypot to collect information from attackers, and the collected data is formed into multiple clusters using the K-means algorithm. Then, the attributes of each cluster are manually tagged through MITRE ATT&CK. The TF-IDF value of each payload is calculated, and the tagged data, data-related information, and TF-IDF calculation score are saved in the Session Table.
|
 ICACT20230048 Slide.05
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.05
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
 |
Moving forward, we'll delve into the Proposed System portion of our presentation. As part of this section, I've broken it into five smaller sub-sections to provide a comprehensive overview of the system we've designed. Each sub-section will be carefully explained in detail, so you'll clearly understand how our system works and the various components that make it up. This section aims to give you an in-depth look at our Proposed System and how it's designed to analyze data.
|
 ICACT20230048 Slide.04
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.04
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
 |
With the rise of the internet in recent years, there has been a proliferation of cyber attacks, big and small. Attackers constantly find new ways to attack victims' computers and steal sensitive information. Our research has aimed to address this problem by designing a system that analyzes the attack information of the attacker. The implementation details will be covered in the next section.
|
 ICACT20230048 Slide.03
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.03
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
 |
In the first part of our presentation, I'd like to start with an introduction.
|
 ICACT20230048 Slide.02
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.02
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
 |
Today's presentation comprises four key segments that I'll be covering. First and foremost, I'll start with an introduction to set the stage for what we'll discuss in greater detail later. After that, I'll delve into the heart of the matter and present my Proposed System.
Next, I'll move on to the analysis and presentation of the results. This is where I'll be showcasing some of the key findings from our research and breaking down the data in a way that's easy to understand.
Finally, I'll summarize the key takeaways from my presentation and discuss the findings' implications.
|
 ICACT20230048 Slide.01
[Big slide for presentation]
[YouTube]
ICACT20230048 Slide.01
[Big slide for presentation]
[YouTube] |
Chrome Text-to-Speach Click!! Click!! |
 |
Hello, everyone. My name is Man Ling, Liao. I’m from National Taiwan University of Science and Technology. Today I’m happy to present our work, An Intelligent Cyber Threat Classification System.
|






